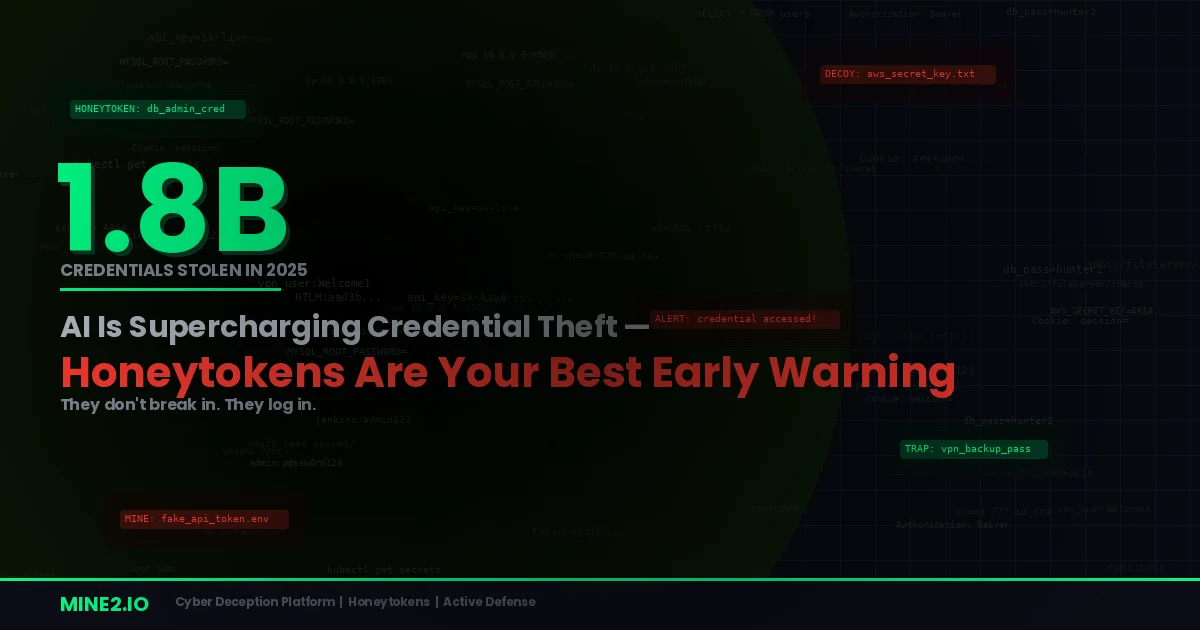
In 2025, infostealers harvested 1.8 billion credentials from 5.8 million compromised endpoints. That's not a typo. According to Flashpoint's Global Threat Intelligence Index, credential-based attacks surged by 160% year-over-year, making stolen identities the single most reliable weapon in the modern attacker's arsenal. Verizon's 2025 DBIR confirms the trend: 22% of all breaches now begin with compromised credentials — overtaking phishing as the dominant initial access vector.
The CrowdStrike 2026 Global Threat Report puts a finer point on it: AI-enabled adversary operations jumped 89% year-over-year, with average eCrime breakout time collapsing to just 29 minutes. The fastest observed breakout? Twenty-seven seconds from initial access to lateral movement.
This isn't tomorrow's problem. It's today's reality. And traditional security tools are losing the race.
The Identity Crisis: Why Credentials Have Become the #1 Attack Vector
The shift from exploit-driven breaches to identity-led intrusions didn't happen overnight, but 2025 was the tipping point. Darktrace's Annual Threat Report 2026 found that identity weaknesses played a material role in nearly 90% of incident response investigations. Unit 42's Global Incident Response Report 2026 echoed this: initial access was driven by identity-based techniques — phishing, stolen credentials, brute force, and insider activity — in 65% of cases.
What changed? Three things converged:
AI-powered infostealers reached industrial scale. Malware families like Lumma, Redline, StealC, and Acreed are now distributed through Malware-as-a-Service platforms, allowing low-skill attackers to deploy credential-harvesting campaigns with minimal effort. Specops analyzed over 6 billion stolen passwords captured from infostealer campaigns during 2025 alone. IBM's X-Force reported that over 300,000 ChatGPT credentials were exposed through infostealers — a signal that AI platforms now carry the same credential risk as enterprise SaaS.
Phishing got frighteningly good. AI-crafted phishing messages are now personalized, long-form, and nearly indistinguishable from legitimate communication. Darktrace observed a 28% increase in QR-code-based phishing (1.2 million attacks), along with novel social engineering techniques growing from 32% to 38% of observed campaigns. Over 8.2 million phishing emails specifically targeted VIP accounts — executives and privileged users whose credentials unlock the widest access.
Attackers don't need exploits anymore. Why burn a zero-day when you can log in? eSentire's 2025 Year in Review documented a 389% rise in account compromise, with credential access representing 75% of all malicious activity observed. The Check Point finding is stark: leaked credentials increased 160% year-over-year, with most compromised accounts being personal — not corporate — often due to password reuse across services.
The result? Once inside, attackers use legitimate tools and permissions to blend into normal activity. Lateral movement is fast, quiet, and nearly invisible to traditional detection stacks.
Why EDR, SIEM, and MFA Aren't Enough
Here's the uncomfortable truth: your existing security stack was designed for a different era.
EDR watches endpoints, not identities. When an attacker logs in with a valid credential, the endpoint sees a legitimate session. There's no malware to detect, no exploit signature to match. The CrowdStrike report documents adversaries using AI-generated scripts to accelerate credential dumping while erasing forensic evidence — all within the time it takes your SOC to triage an alert.
SIEM drowns in noise. With the cybersecurity industry facing a 4.8 million worker shortage, SOC teams are already buried in alert fatigue. When the attacker's activity looks identical to normal user behavior, SIEM rules don't fire. By the time anomaly detection correlates enough signals, data exfiltration may already be complete — Unit 42 observed the fastest quarter of intrusions reaching exfiltration in just 72 minutes in 2025, down from 285 minutes in 2024.
MFA is being bypassed at scale. Phishing-as-a-Service kits like Tycoon2FA, FlowerStorm, and EvilProxy are purpose-built to intercept MFA tokens in real time. eSentire found these PhaaS kits are comprehensive, continuously updated offerings designed to bypass modern MFA controls. Session hijacking through stolen authentication cookies renders MFA meaningless after the initial login.
The fundamental problem? These tools are reactive. They detect attacks after something bad happens on a real system. The damage window — the gap between initial access and detection — is where breaches metastasize.
The Deception Advantage: Why Honeytokens Detect What Others Can't
Cyber deception flips the detection model entirely. Instead of waiting for malicious behavior on production assets, you plant decoy credentials, documents, and services across your environment. Any interaction with these decoys is, by definition, unauthorized — generating an immediate, high-fidelity alert with zero false positives.
Here's why deception is uniquely effective against the credential theft epidemic:
Honeytokens Catch Credential Harvesters in the Act
When an infostealer scrapes a compromised endpoint for stored credentials, it doesn't distinguish between real and fake. Mine2 honeytokens — fake AWS keys planted in environment variables, bogus database connection strings in config files, decoy API tokens in code repositories — get swept up alongside legitimate secrets. The moment an attacker attempts to use a honeytoken, the alert fires. No behavioral analysis required. No anomaly scoring. No waiting for correlation.
This is especially powerful against the infostealer supply chain. Credentials stolen by Lumma or Redline end up on dark web markets, where they're purchased by other threat actors. When those buyers attempt to use a honeytoken that was harvested months ago, the deception still works — creating a persistent, long-lived early warning system.
Decoy Services Expose Lateral Movement Instantly
Once attackers are inside a network with valid credentials, their next move is reconnaissance — scanning for accessible services, open ports, and exploitable targets. Mine2's MineField deploys decoy TCP services that look and respond like real production systems. Any connection attempt is an instant indicator of compromise, catching lateral movement that EDR and network monitoring would classify as normal internal traffic.
Cloud Mines Detect Cloud Credential Abuse
With 94% of organizations relying on cloud infrastructure and Azure alone attracting 43.5% of observed malware samples (per Darktrace), cloud credential theft is an acute risk. Mine2's Cloud Mines scatter fake AWS resources — decoy S3 buckets, phantom IAM roles, bogus Lambda functions — across your cloud environment. When compromised cloud credentials are used to enumerate resources, Cloud Mines trigger before any real asset is touched.
Zero False Positives — The SOC's Best Friend
The deception technology market is projected to grow from $2.21 billion in 2024 to $5.61 billion by 2032 (Verified Market Research) — and the zero-false-positive advantage is a major reason why. In a world where SOC teams are drowning in alerts and the talent gap is widening, a detection mechanism that only fires on actual malicious activity is transformational. Every honeytoken alert is actionable. Every decoy interaction demands investigation.
Practical Playbook: Deploying Honeytokens Against Credential Theft
Here's how to start building a deception layer into your credential defense strategy:
1. Seed Honeytokens Where Infostealers Harvest
Plant fake credentials in the locations attackers and their malware target first: browser credential stores, environment variables, .env files, AWS credentials files (~/.aws/credentials), SSH key directories, and config files. These are the exact locations infostealers scrape — making them ideal honeytoken placement points.
2. Deploy Decoy Credentials in Active Directory
Create honeytoken accounts in Active Directory with enticing names — svc_backup_admin, sql_replication, legacy_vpn — that look like high-value service accounts. When an attacker performing credential harvesting via tools like Mimikatz or DCSync attempts to use these accounts, you get an immediate alert and a strong signal of active directory compromise.
3. Scatter Fake Secrets in Code Repositories
Embed honeytoken API keys and database connection strings in internal Git repositories, CI/CD pipeline configs, and documentation wikis. This catches both external attackers who have gained repo access and insider threats conducting unauthorized reconnaissance.
4. Deploy MineField Across Network Segments
Place decoy services on unused IP addresses and ports across your network segments. This creates a tripwire for any port scanning or lateral movement activity — catching behavior that would otherwise blend into normal network traffic.
5. Extend Deception into Cloud Environments
Use Mine2's Cloud Mines to generate fake resources across your AWS footprint. Attackers who gain cloud credentials will naturally enumerate available resources — and the first decoy they hit becomes your earliest warning.
6. Wire Deception Alerts into Your SOC Workflow
Integrate honeytoken alerts with your existing SIEM and SOAR platforms to trigger automated response workflows — isolating compromised endpoints, revoking credentials, and initiating incident response before the attacker reaches real assets.
The Bottom Line
The credential theft epidemic is accelerating. AI is making attackers faster, stealthier, and more capable than ever. Traditional defenses — EDR, SIEM, MFA — remain necessary but insufficient against identity-led intrusions where attackers log in rather than break in.
Cyber deception, and honeytokens specifically, address the fundamental gap: they detect credential abuse at the moment of use, with zero false positives and no dependence on behavioral baselines. In a threat landscape where breakout times are measured in seconds and stolen credentials number in the billions, that kind of early warning isn't optional — it's essential.
The organizations that survive the AI-accelerated threat era won't be the ones with the biggest security budgets. They'll be the ones who made the attacker's stolen intelligence unreliable — turning every credential cache, every network scan, and every cloud enumeration into a potential tripwire.
Ready to turn your credential landscape into a minefield for attackers? See how Mine2's honeytokens work →
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Need Security Help?
Protect your organization with MINE2's cyber deception platform.