The latest threat intelligence reports from 2026 paint a stark picture: attackers no longer need malware to own your network. They log in.
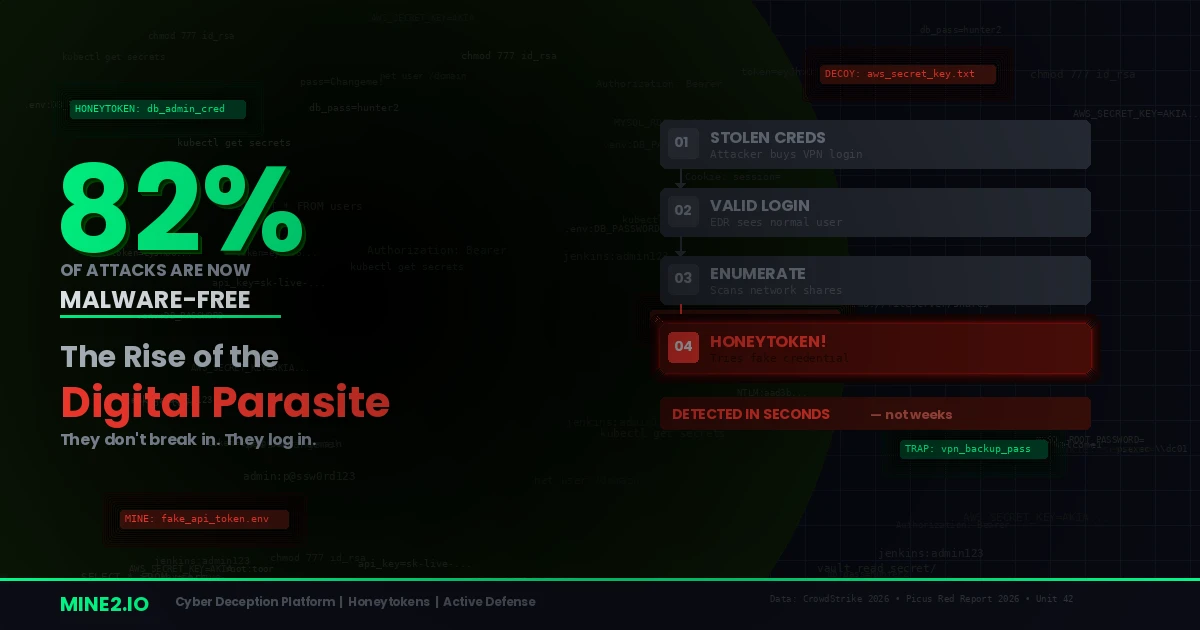
CrowdStrike's 2026 Global Threat Report revealed that 82% of all detections in 2025 were malware-free—meaning adversaries relied on stolen credentials, valid accounts, and legitimate tools to move through environments undetected. The average eCrime breakout time dropped to just 29 minutes, with the fastest recorded at a staggering 27 seconds.
Picus Security's Red Report 2026 coined a term for this new breed of attacker: the Digital Parasite—intrusions designed for quiet persistence rather than immediate, visible damage. These attackers prioritize identity-based access, low-noise execution, and prolonged operation inside an organization's trusted environments.
The question every security team must ask: If the attacker looks like a legitimate user, how do you detect them?
The Death of the Malware Signature
For decades, cybersecurity has been built around detecting malicious code—antivirus signatures, endpoint detection rules, sandbox analysis. But adversaries have evolved past this model entirely.
Here's what the data tells us:
- 82% of intrusions involved no malware at all (CrowdStrike 2026)
- Identity weaknesses played a material role in almost 90% of incident response investigations (Unit 42 Global IR Report 2026)
- 65% of initial access was achieved through identity-based techniques—phishing, stolen credentials, brute force, and insider activity (Unit 42)
- Valid Accounts (T1078) succeeded in 98% of tested environments, indicating credential-based access is rarely stopped after initial compromise (Picus Blue Report 2025)
- Credentials from Password Stores (T1555) appeared in 23.49% of attacks, confirming the shift toward quieter credential theft (Picus Red Report 2026)
The pattern is unmistakable. Attackers aren't breaking down the door—they're walking through it with a stolen key. And once inside, they blend in with normal operations, making detection nearly impossible with traditional tools.
Why Traditional Defenses Fail
EDR/XDR solutions excel at detecting malicious binaries, suspicious process chains, and known attack patterns. But when an attacker authenticates with valid credentials and uses built-in system tools—PowerShell, RDP, WMI—these solutions see normal administrative activity.
SIEM platforms can correlate logs, but identity-based attacks generate authentication events that look identical to legitimate logins. A compromised VPN credential from a dark web marketplace, used during business hours from a plausible geolocation, triggers zero alerts.
Firewalls and Network Security protect the perimeter, but the perimeter is meaningless when the attacker has valid credentials. They're already inside.
The Picus Red Report 2026 documents this perfectly: stealth today is not just about evasion—it's about restraint. Modern attackers don't trigger alarms because they don't need to do anything alarming. They log in, enumerate, and exfiltrate—all using tools your IT team uses every day.
The Infostealer Supply Chain: $50 for Full Access
The underground credential economy has industrialized. Modern infostealers like Lumma, Vidar, and Banshee don't just harvest passwords—they capture browser sessions, cookies, saved credentials, and system-level files that allow attackers to fully impersonate victims.
A Specops analysis of over 90,000 infostealer dumps containing 800 million+ rows of data revealed that attackers can now associate stolen credentials with specific individuals, their employers, and their roles within an organization. A single compromised personal device can cascade into full enterprise access.
And it starts as cheaply as $50 for VPN credentials on a dark web marketplace—complete with seller ratings and refund policies.
Infostealers harvested approximately 1.8 billion credentials in 2025 alone. The supply is massive, the cost is negligible, and the impact is devastating. This is the fuel that powers the Digital Parasite.
Why Honeytokens and Cyber Deception Are the Answer
If attackers look like legitimate users, the only reliable detection method is giving them something irresistible that no legitimate user would ever touch.
This is the fundamental principle behind cyber deception—and specifically, honeytokens.
How It Works
Mine2's cyber deception platform plants digital landmines throughout your environment—fake credentials, decoy documents, bogus API keys, fabricated database entries, and decoy services. These assets look authentic to an attacker performing reconnaissance but are never used in normal operations.
The moment an attacker interacts with a honeytoken—tries a fake credential, opens a decoy document, queries a fabricated database—an alert fires with zero ambiguity. No false positives. No legitimate user would access these assets because they aren't part of any real workflow.
Why Deception Defeats the Digital Parasite
Consider the attack chain that EDR, SIEM, and firewalls all miss:
- Initial Access: Attacker buys stolen VPN credentials → logs in normally → EDR sees nothing
- Credential Harvesting: Attacker enumerates network shares, finds a file with database credentials → SIEM logs routine file access
- Lateral Movement: Attacker uses found credentials to access production database → Firewall allows internal traffic
- Data Exfiltration: Attacker slowly exports customer records → All tools see authorized user activity
Now add Mine2's deception layer:
- Initial Access: Attacker logs in with stolen credentials → same as above
- Credential Harvesting: Attacker finds a honeytoken credential file planted by Mine2 → tries it → 🚨 INSTANT ALERT
- Investigation begins immediately — full attacker context captured before any real damage
The attacker's greatest strength—blending in with legitimate users—becomes their fatal weakness. They can't distinguish real credentials from honeytokens, and their natural instinct to harvest and test every credential they find guarantees interaction with the deception layer.
The Numbers That Matter
- Mean Time to Detect with traditional tools: days to weeks (Unit 42 found attackers persisting for extended periods)
- Mean Time to Detect with honeytokens: seconds (the instant a fake credential is used)
- False positive rate with SIEM/EDR: high (alert fatigue is a leading cause of missed detections)
- False positive rate with honeytokens: effectively zero (no legitimate user touches these assets)
Defending Against the Digital Parasite: A Practical Playbook
Based on the 2026 threat intelligence landscape, here's how organizations should layer their defenses:
1. Deploy Deception at Every Layer
Plant honeytokens across endpoints, network shares, cloud environments, and code repositories. Mine2's single-click deployment makes this operational in under a week with zero impact on production systems.
2. Treat Identity as Critical Infrastructure
Implement phishing-resistant MFA (FIDO2/passkeys), enforce least-privilege access, and add Identity Threat Detection and Response (ITDR) to your stack.
3. Assume Breach, Detect Early
With 82% of attacks being malware-free, your detection strategy must go beyond malware signatures. Deception-based detection catches what EDR and SIEM cannot.
4. Monitor the Credential Supply Chain
Track your organization's exposure on dark web marketplaces and infostealer dump sites. Rotate compromised credentials immediately.
5. Compress Your Response Window
With breakout times as low as 27 seconds, every minute of detection delay is catastrophic. Honeytokens provide the earliest possible warning—before lateral movement even begins.
The Bottom Line
The era of the Digital Parasite is here. Attackers have evolved past malware, past perimeter defenses, and past signature-based detection. They use your own credentials, your own tools, and your own trust model against you.
The only defense that works against an attacker who looks legitimate is an environment where touching the wrong asset instantly reveals them.
That's cyber deception. That's Mine2.
Ready to catch the parasites in your network? Deploy Mine2's honeytokens and detect intrusions on day zero—before attackers reach anything real.
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
AI Is Supercharging Credential Theft — Here's Why Honeytokens Are Your Best Early Warning
Kerberoasting in April 2026: Why CVE-2026-20833 Enforcement Is Not Enough Without AD Mines
The Infostealer Epidemic: 642 Million Stolen Credentials Are Already Inside Your Enterprise
Need Security Help?
Protect your organization with MINE2's cyber deception platform.