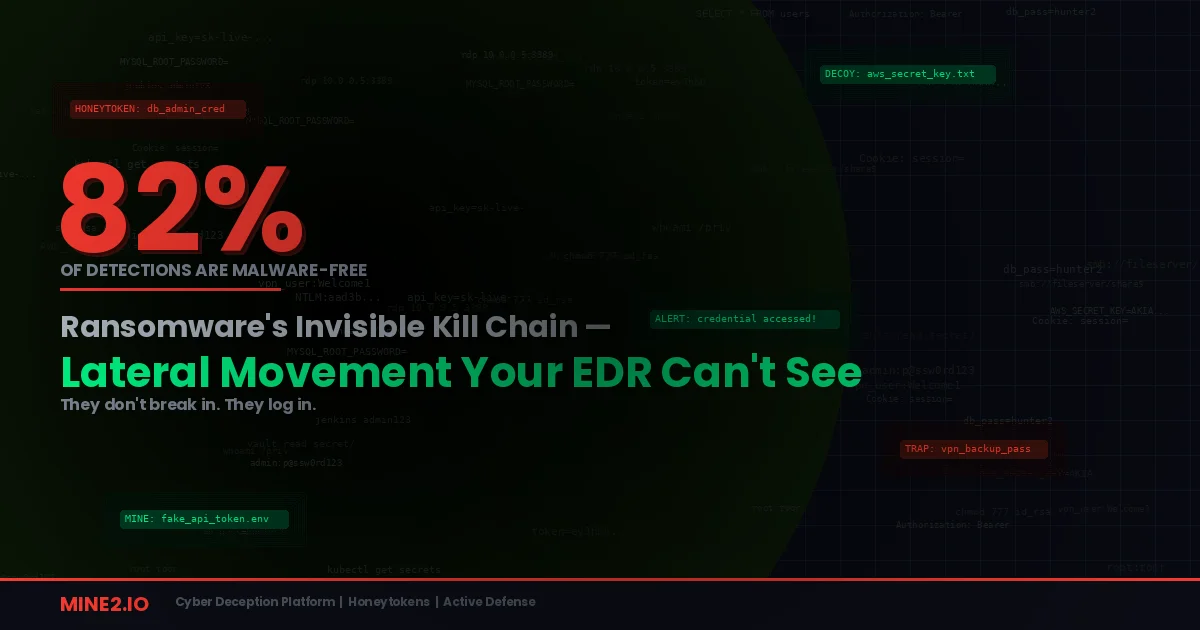
Here's a stat that should keep every CISO up at night: 82% of threat detections in 2025 were malware-free. That's straight from the CrowdStrike 2026 Global Threat Report. No malicious binaries. No exploit signatures. Just adversaries logging in with valid credentials and using your own administrative tools — PowerShell, PsExec, WMI, RDP — to walk through your network undetected.
Ransomware attacks surged 58% in 2025, with over 7,500 victims publicly named on data leak sites. Groups averaged nearly 700 new victims per month in the final quarter. The average cost of a ransomware breach hit $5.08 million. And according to Chainalysis, even as total ransom payments dropped to $820 million (with only 28% of victims paying), the median ransom demand exploded 368% to nearly $60,000 — proving that fewer organizations are paying, but the ones that do are paying far more.
The uncomfortable truth? The initial access was survivable. In nearly every major ransomware incident, it's the lateral movement phase — the quiet walk through the network using legitimate tools — that turns a compromised endpoint into a domain-wide catastrophe.
The Living-off-the-Land Playbook: How Ransomware Moves Without Malware
Modern ransomware operators have perfected what the industry calls living-off-the-land (LOTL) techniques. Instead of deploying custom malware that EDR tools are trained to detect, they abuse the same administrative utilities that your IT team uses every day.
The numbers paint a grim picture. According to the Picus Security 2025 Red Report, PowerShell appeared in 71% of all living-off-the-land attacks, making it the most common post-compromise tool across ransomware families. Sophos found that RDP abuse was present in 90% of ransomware cases. Legitimate remote management tools — AnyDesk, Atera, ScreenConnect, Splashtop — are being weaponized across multiple ransomware operations for persistent access.
The CrowdStrike report documented the consequences: the average eCrime breakout time collapsed to just 29 minutes, with the fastest observed breakout at 27 seconds. Unit 42's data shows the fastest quarter of intrusions reaching data exfiltration in 72 minutes in 2025 — down from 285 minutes in 2024.
The kill chain is remarkably consistent across groups. Researchers tracking dozens of active ransomware operations describe a repeatable pattern: phish the user or buy brokered access, execute via PowerShell, persist with valid accounts or scheduled tasks, move laterally via RDP and PsExec, exfiltrate over C2 channels, delete backups, and encrypt. The entire lateral movement phase relies on tools and protocols that are indistinguishable from normal IT operations.
This is why the shift from exploit-driven breaches to identity-led intrusions matters so much. Darktrace's Annual Threat Report 2026 found that attackers increasingly use legitimate tools and permissions to disguise their activity as normal behavior, making lateral movement fast and difficult to detect. When PsExec, WinRM, and RDP are the attacker's weapons, your detection tools face an impossible task: separating malicious administrative activity from legitimate administrative activity in real time.
Why Your Current Stack Is Losing This Battle
Let's be direct about the detection gap.
EDR is built for malware, not lateral movement. When a ransomware affiliate uses PsExec to execute commands on a remote system, the endpoint sees a legitimate administrative action. There's no signature to match, no behavioral anomaly to flag — it's the same tool your sysadmin used five minutes earlier. CrowdStrike's own data confirms this: 82% of detections were malware-free. The ransomware ecosystem's most effective tactic is one that renders traditional endpoint detection functionally blind.
Network monitoring drowns in east-west traffic. Most enterprise networks still rely on perimeter-focused architectures. The internal network is flat, or segmented into broad VLANs that don't restrict lateral traffic between devices in the same zone. When an attacker moves from one workstation to another using RDP, it looks exactly like a remote desktop session from an authorized user — because technically, it is.
SIEM rules can't keep up with LOTL. The detection gap for living-off-the-land techniques is well-documented. Spearphishing Link (MITRE T1566.002) has one of the most critical detection gaps, with only a handful of Sigma rules despite being used by dozens of threat actors. Seven ATT&CK techniques have no D3FEND defensive mappings at all, concentrated in the Impact, Persistence, and Lateral Movement phases — exactly where ransomware does its damage.
The talent gap amplifies everything. The cybersecurity industry faces a 4.8 million worker shortage globally. SOC teams are drowning in alert fatigue, and 40% of ransomware victims in 2025 cited lack of cybersecurity expertise as a contributing factor to their breach. Another 39% cited insufficient staff or capacity. When your team doesn't have the headcount to investigate every alert, false-positive-heavy detection tools become a liability.
The result? Ransomware operators have an average of 73 days of unrestricted access before being removed. And 57% of ransomware incidents in Q4 2024 were first detected by external parties — not the organization's own security team.
How Deception Technology Catches Lateral Movement That Detection Can't
Cyber deception solves the lateral movement problem from a fundamentally different angle. Instead of trying to distinguish malicious LOTL activity from legitimate administration — an increasingly impossible task — deception places decoy assets along the paths attackers must traverse. Any interaction with a decoy is, by definition, unauthorized.
Zero noise. Zero false positives. Immediate, high-fidelity signal that someone is moving where they shouldn't be.
Decoy Services Become Tripwires for Port Scanning and Reconnaissance
The first thing a ransomware affiliate does after gaining initial access is reconnaissance — scanning for accessible services, open ports, and exploitable systems. Mine2's MineField deploys decoy TCP services across your network that look and respond like real production systems. When an attacker's scanning tools hit a decoy service — and they will, because attackers scan broadly and indiscriminately — the alert fires instantly.
This is critical because reconnaissance happens before the attacker uses any LOTL tool. Before PowerShell. Before PsExec. Before RDP lateral movement. MineField detects the intent to move laterally before the movement itself begins, giving your team a head start measured in minutes or hours rather than the 29-minute breakout window that EDR is already struggling to match.
Honeytoken Credentials Catch Privilege Escalation
Ransomware playbooks depend on credential harvesting. Tools like Mimikatz for NTLM credential theft and DCSync for Active Directory replication are standard issue across ransomware operations. Mine2 honeytokens — fake service accounts planted in Active Directory, decoy credentials stored in LSASS-accessible locations, bogus admin credentials in Group Policy Preferences — get harvested alongside real credentials.
When the attacker attempts to authenticate with a honeytoken, the alert fires. No behavioral analysis needed. No anomaly scoring. The honeytoken is fake — any attempt to use it is definitively malicious. This cuts through the fundamental LOTL detection challenge: you no longer need to determine whether PsExec is being used legitimately or maliciously. You just need to know that someone used a credential that shouldn't exist.
Fake Shared Drives and Documents Detect Data Staging
Before encryption or exfiltration, ransomware operators stage data. They enumerate file shares, identify high-value targets, and prepare for the final payload. Mine2 honeytokens include decoy file shares and sensitive-looking documents — fake financial records, bogus employee databases, fabricated strategic plans — planted across your network.
When an attacker or automated tool accesses these decoys during the data staging phase, you get an immediate alert. This is especially powerful against the growing trend of data-only extortion — which now appears in 74% of ransomware attacks — where attackers skip encryption entirely and focus on stealing data for leverage.
Cloud Mines Close the Cloud Lateral Movement Gap
Cloud compromise has become a primary entry point for ransomware. Darktrace found that 58% of European incidents and a majority of American incidents began with compromised cloud accounts. Once inside cloud infrastructure, attackers enumerate resources, escalate privileges, and pivot between services. Mine2's Cloud Mines scatter fake AWS resources — decoy S3 buckets, phantom IAM roles, bogus Lambda functions — across your cloud environment. Any enumeration attempt that touches a Cloud Mine generates an immediate alert, catching cloud-based lateral movement before real assets are reached.
Practical Playbook: Building a Deception Layer Against Ransomware
Here's how to deploy deception technology specifically to counter the ransomware lateral movement playbook:
1. Map Your Attack Surface and Plant Decoys on Likely Pivot Points
Ransomware operators target predictable network paths: domain controllers, file servers, backup systems, database servers. Place MineField decoy services on IP addresses adjacent to these high-value targets. When attackers scan the subnet looking for their next hop, the decoy fires first.
2. Seed Honeytoken Credentials in Credential Harvesting Locations
Plant fake credentials in the exact locations Mimikatz and similar tools scrape: LSASS process memory, cached domain credentials, Group Policy Preferences, and credential manager stores. Create AD honeytoken accounts with names that look like high-value service accounts — svc_sql_prod, backup_admin, dc_replication. Any attempt to use these triggers immediate investigation.
3. Deploy Decoy File Shares Across Critical Segments
Create realistic-looking network shares with enticing names — \\fileserver\HR_Confidential, \\nas01\Financial_Reports — and populate them with honeytoken documents. When ransomware operators enumerate shares during data staging, any access to these decoys reveals their presence.
4. Harden with Fortify, Then Layer Deception
Use Mine2's Fortify to close the low-hanging configuration gaps — unnecessary services, weak permissions, exposed admin interfaces — that make lateral movement easy. Then layer deception on top, so that even if an attacker finds a gap you missed, the next step they take hits a tripwire.
5. Integrate Deception Alerts with Automated Containment
Wire MineField and honeytoken alerts into your SOAR platform to trigger automated response: isolate the source endpoint, disable the compromised account, revoke active sessions, and escalate to your incident response team. The zero-false-positive nature of deception alerts means automated containment won't disrupt legitimate operations — every alert is real.
6. Cover the Cloud Pivot Path
Deploy Cloud Mines across your AWS environment, with particular focus on IAM enumeration and S3 bucket discovery. As cloud credentials increasingly become the first foothold for ransomware, your deception layer must extend beyond on-premise networks.
The Bottom Line
Ransomware's most dangerous phase isn't the initial compromise — it's the invisible lateral movement that follows. With 82% of detections being malware-free and breakout times shrinking to seconds, the industry's reliance on signature-based and behavioral detection alone is a losing strategy.
Deception technology doesn't try to win the impossible game of distinguishing legitimate PsExec from malicious PsExec. Instead, it plants tripwires that only fire when someone does something no authorized user should ever do — accessing a decoy service, using a fake credential, opening a honeytoken document. In a threat landscape where ransomware victims average 73 days of attacker dwell time and 57% of incidents are discovered by external parties, that kind of guaranteed-signal detection isn't a nice-to-have. It's the early warning system that determines whether your incident is a contained endpoint compromise or a full-domain ransomware event.
The organizations that survive the ransomware epidemic won't be the ones who built higher walls. They'll be the ones who turned their network into a minefield — where every wrong step the attacker takes ends the intrusion before it begins.
Ready to stop ransomware at the lateral movement phase? See how Mine2's deception platform works →
mine2 team
The MINE2 team consists of cybersecurity experts, researchers, and engineers dedicated to advancing threat detection and cyber deception technologies.
Recent Articles
Your EDR Is Dead — Now What? Why Deception Is the Detection Layer That Survives EDR Killers
When Defenders' Tools Become Attack Vectors: The Management Platform Exploitation Crisis
The AI Agent Credential Heist: How TeamPCP Weaponized LiteLLM to Loot Cloud Environments
Need Security Help?
Protect your organization with MINE2's cyber deception platform.